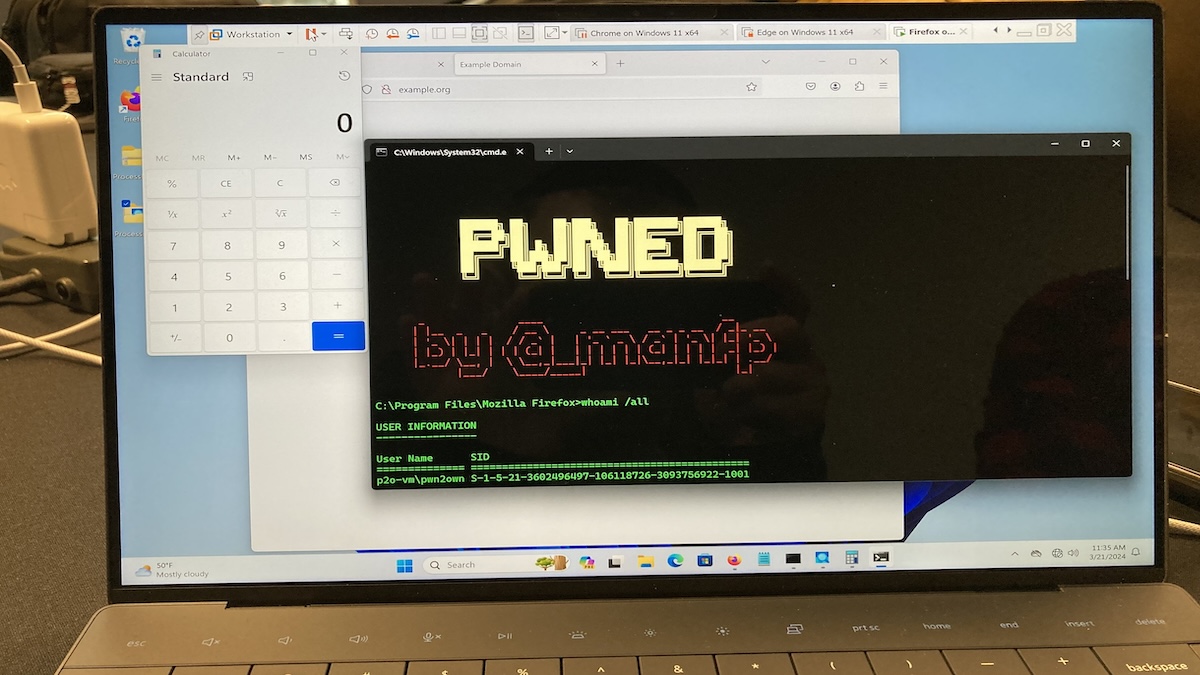
Mozilla has released Firefox browser updates to patch two zero-day vulnerabilities that were exploited at the Pwn2Own Vancouver 2024 hacking contest last week.
The issues, discovered by security researcher Manfred Paul, were chained together to escape the browser’s sandbox and execute code on the system.
Tracked as CVE-2024-29943, the first vulnerability is described as an out-of-bounds access flaw that leads to the bypass of range analysis.
“An attacker was able to perform an out-of-bounds read or write on a JavaScript object by fooling range-based bounds check elimination,” Mozilla explains in its advisory.
The second bug, CVE-2024-29944, is a privileged JavaScript execution issue in event handlers, leading to a sandbox escape.
“An attacker was able to inject an event handler into a privileged object that would allow arbitrary JavaScript execution in the parent process,” Mozilla says.
CVE-2024-29944, Mozilla notes, affects the desktop version of Firefox only, and cannot be exploited against the mobile app.
Mozilla says both vulnerabilities are ‘critical severity’ bugs, without providing a CVSS score for either of them.
On Friday, Mozilla released Firefox 124.0.1 with patches for both issues and Firefox ESR 115.9.1 with fixes for CVE-2024-29944. Both vulnerabilities were exploited and disclosed at Pwn2Own the day before.
“Manfred Paul used an OOB Write for the RCE and an exposed dangerous function bug to achieve his sandbox escape of Mozilla Firefox,” Trend Micro’s Zero Day Initiative (ZDI) said on Thursday.
Participants at the hacking contest earned over $1.1 million, with Paul declared the winner of this Pwn2Own, after also hacking the Safari, Chrome, and Edge browsers, and earning over $200,000 in bug bounty rewards. He received $100,000 for the two Firefox zero-days.
Related: Chrome 123, Firefox 124 Patch Serious Vulnerabilities
Related: Chrome 122, Firefox 123 Patch High-Severity Vulnerabilities